AWS Collector Deployments
Collectors can be deployed directly on AWS using a template. Here are the details and security requirements for that installation.
Deploying a collector to a AWS
- Login to the BindPlane account to be used
- Navigate to the Collectors page
- Click the Add Collector button located at the top right of the page
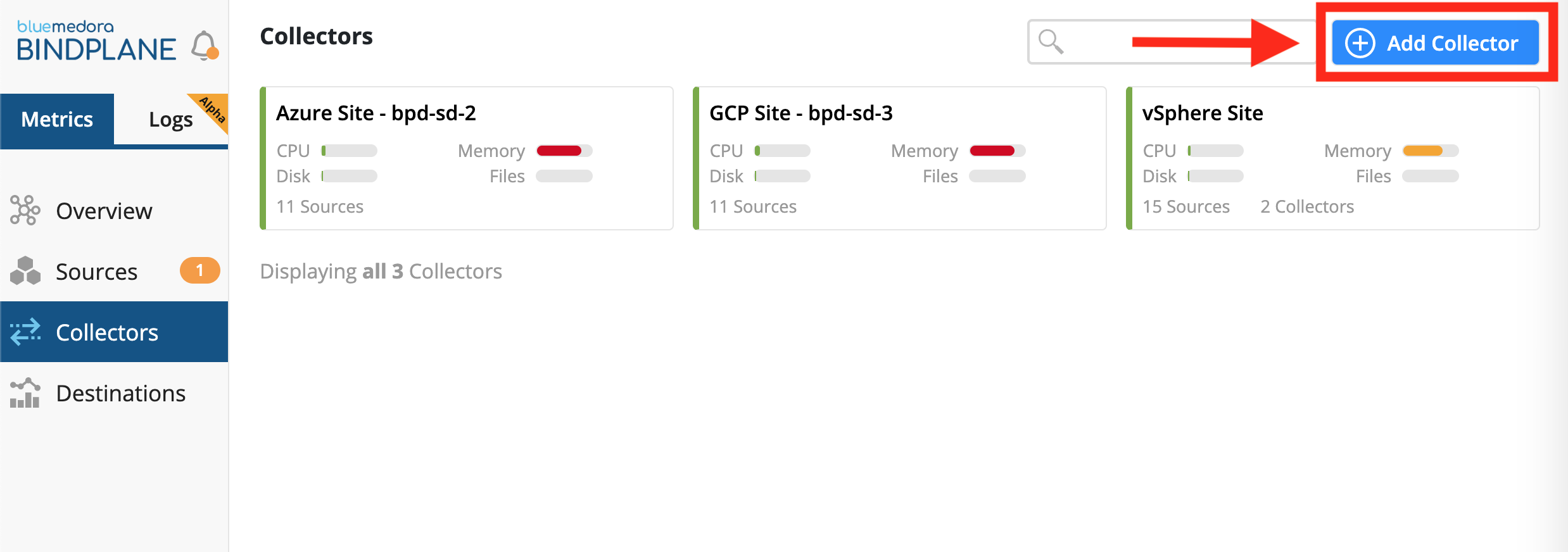
Collectors Page & Button to Add Collector
- For the platform, choose Amazon Web Services
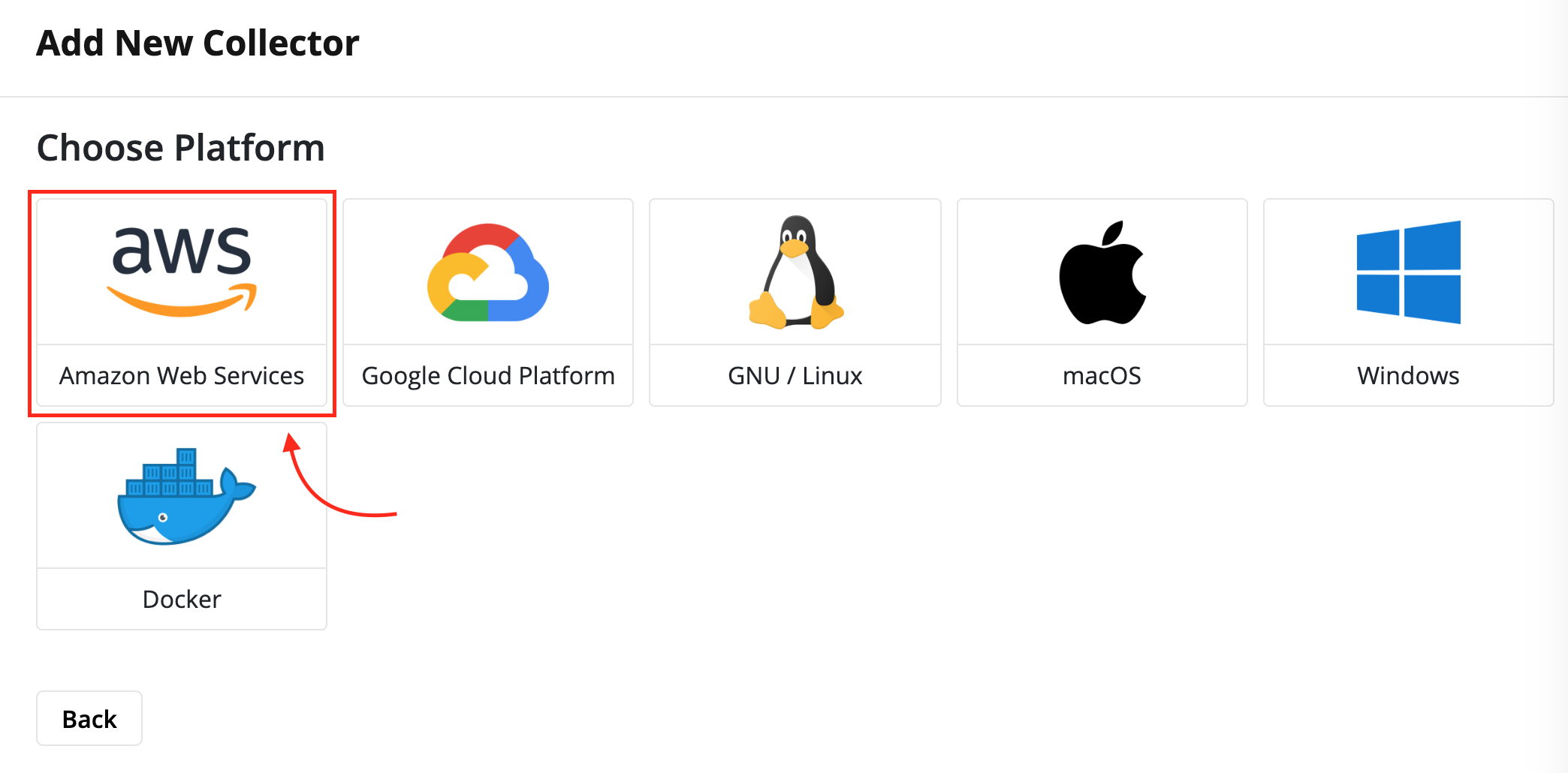
Choosing a platform to deploy a BindPlane Collector
- Select the region to deploy the Collector in.
- Click the Launch Stack button.
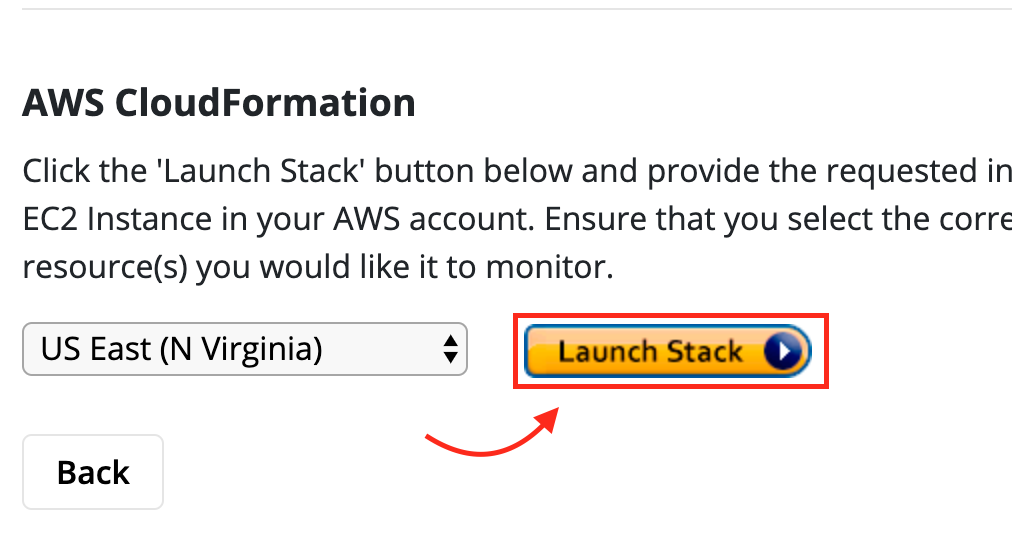
Button that directs the user to launch a stack
VPC/Subnet Combination Warning!
The most common issue, so far, when deploying a collector AWS, has been users selecting the incorrect VPC/Subnet combination. Amazon does not filter out the subnets per VPC and it is very easy to make a mistake. Below we have descriptions to help avoid running into this issue.
Which Subnet?
The subnet in the VPC you’re lanuching the instance into. Verify this subnet belongs to the VPC you specified above.Which Security Group?
The security group the instance should belong to. Verify this security group belongs to the VPC specified above.Key Pair:
The key pair for access the instance via SSH. If none exist, you may need to create a keypair under EC2 -> Key Pairs in the AWS console.
- Fill out the required information for the Create Stack form
- Click the Create Stack button.
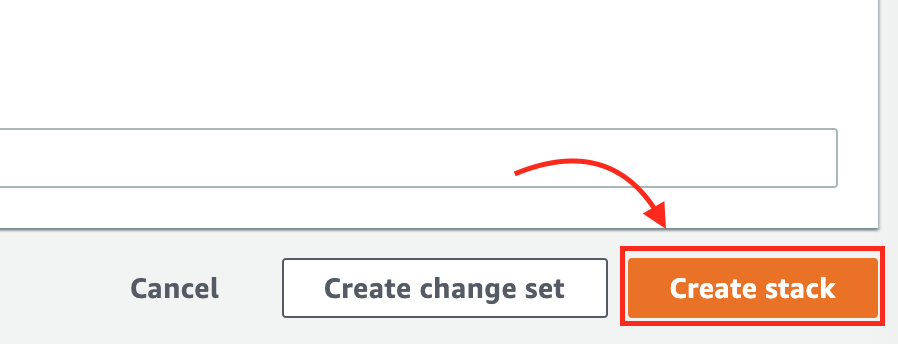
Button to create a Stack
Network Requirements
Once the collector is installed it only needs the following network access:
-
The ability to make outbound connections to all systems being monitored. This includes APIs for various cloud providers, if needed.
-
The ability to make outbound connections to
https://production.api.bindplane.bluemedora.com:443to send collection data back to BindPlane, as well as to retrieve configuration information.
IP Address Fluctuation
The IP address of
https://production.api.bindplane.bluemedora.com:443can change. The endpoint can exist anywhere within theus-east-1region on AWS.To retrieve a list of subnets that are covered, run the following commands:
wget https://ip-ranges.amazonaws.com/ip-ranges.json cat ip-ranges.json | jq '[.prefixes[]|select(.region=="us-east-1")]' | jq -r '.[].ip_prefix'> aws-useast1-ranges.txt
Least Privileged User
The only requirement to deploy a collector to AWS is that the account attempting to deploy the collector has the permissions necessary to deploy CloudStack templates.
Updated over 4 years ago
