Palo Alto Networks
Monitor Palo Alto Next-Generation Firewalls Virtual and Physical Appliances
This source has been deprecated
observIQ is in the process of transitioning a subset of BindPlane's monitoring capabilities to the observIQ OpenTelemetry Collector. As a result, this Source is no longer publicly available in BindPlane. If you need access to this Source, please reach out to our support via chat or via [email protected].
Data Collection Setup
Metrics are collected via REST API running on PAN-OS.
Network Requirements
Port: 443 (TCP) HTTPS connection to the PAN-OS on the monitored firewall appliance.
Least Privileged User
The least-privileged user (LPU) must be assigned the Admin role and the following XML API permissions:
- Operational Requests
- Logs
- Configuration.
Assigning Palo Alto User Permissions
This topic outlines the required permissions for a Palo Alto Networks least-privileged user (LPU).
- Select Device -> Admin Roles to define your Admin Role profile.
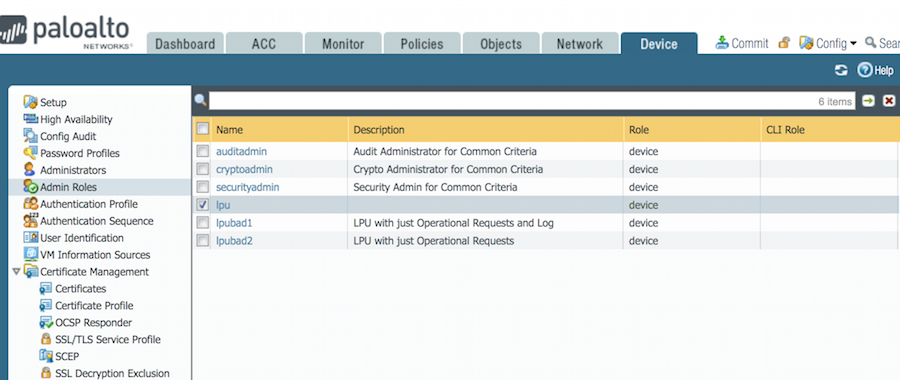
- Select your defined Admin Role.
- In the Admin Role Profile window, click the XML API tab, and ensure Log, Configuration, and Operational Requests permissions are enabled.
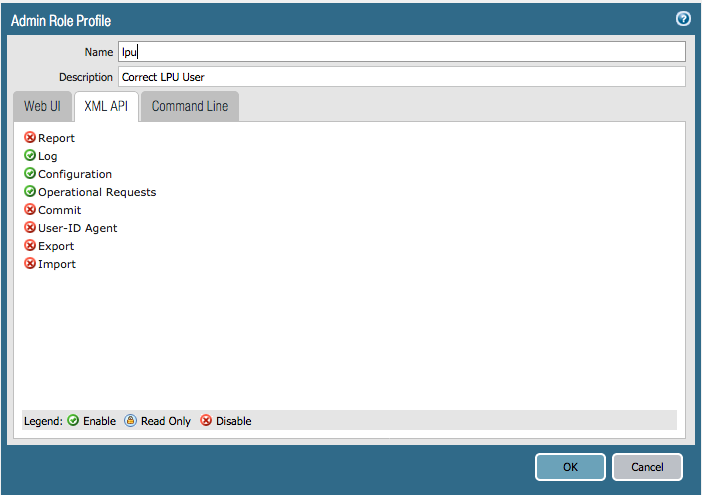
Web UI and Command line permissions are not required.
Supported Versions
Hardware: Palo Alto Next-Generation Firewall
Software: PAN-OS versions 7.1, 8.0 (Virtual and Hardware editions)
Connection Parameters
| Name | Required? | Description |
|---|---|---|
| Host | Required | The Palo Alto Networks Next Generation Firewall to connect to. |
| Port | The port for communication to the Palo Alto Networks Next Generation Firewall. | |
| Username | Required | |
| Password | Required | |
| SSL Configuration | The SSL mode to use when connecting to the target. Can be configured to not use SSL (No SSL), use SSL but do not verify the target's certificate (No Verify), and use SSL and verify the target's certificate (Verify). | |
| Connection Timeout (seconds) | The number of seconds to allow for connecting to the target. | |
| Threat Event Keep Alive Time (hours) | The time in hours to keep threat events alive. | |
| Minimum Event Severity | Events with a severity level below this minimum will not be returned. |
Metrics
Application
| Name | Description |
|---|---|
| Changes | Changes |
| Name | Name |
| Packet Throughput (Packets) | Packet Throughput |
| Sessions (Sessions) | Sessions |
| Threats | Threats |
| Throughput (Bytes) | Throughput |
| VSYS | VSYS |
Fan
| Name | Description |
|---|---|
| Alarm | Alarm |
| Minimum Speed (Rotations per Minute) | Minimum Speed |
| Name | Name |
| Slot | Slot |
| Speed (Rotations per Minute) | Speed |
Firewall
| Name | Description |
|---|---|
| Active BCAST (Sessions) | Active BCAST |
| Active BCAST Sessions (%) | Active BCAST sessions as a percent of active sessions |
| Active ICMP (Sessions) | Active ICMP |
| Active ICMP Sessions (%) | Active ICMP sessions as a percent of active sessions |
| Active MCAST (Sessions) | Active MCAST |
| Active MCAST Sessions (%) | Active MCAST sessions as a percent of active sessions |
| Active Predict (Sessions) | Active Predict |
| Active Predict Sessions (%) | Active predict sessions as a percent of active sessions |
| Active Sessions (Sessions) | Active Sessions |
| Active TCP (Sessions) | Active TCP |
| Active TCP Sessions (%) | Active TCP sessions as a percent of active sessions |
| Active UDP (Sessions) | Active UDP |
| Active UDP Sessions (%) | Active UDP sessions as a percent of active sessions |
| App Version | App Version |
| AV Version | AV Version |
| Average Load 15 Minutes | Average load over the last 15 minutes |
| Average Load 1 Minute | Average load over the last minute |
| Average Load 5 Minutes | Average load over the last 5 minutes |
| Buffer Memory (Kibibytes) | Buffer Memory |
| Connection Establish Rate (Connections per Second) | Connection Establish Rate |
| Control Plane Receive Rate (Packets per Second) | Received from Control Plane |
| CPU Busy (%) | CPU Busy |
| CPU Hardware Interrupts (%) | Percentage of CPU processing time spent servicing hardware interrupts. |
| CPU Idle (%) | Percentage of CPU processing time spent idle. |
| CPU Kernel Processes (%) | Percentage of CPU processing time spent running process handled by the kernel. |
| CPU Niced User Space Processes (%) | Percentage of CPU processing time spent running user space processes that have been niced. |
| CPU Software Interrupts (%) | Percentage of CPU processing time spent servicing software interrupts. |
| CPU Stolen (%) | Percentage of CPU processing time spent waiting for the hypervisor to service another CPU. |
| CPU User Space Processes (%) | Percentage of CPU processing time spent running user space processes such as shells, web servers, and applications. |
| CPU Wait (%) | Percentage of CPU processing time spent waiting for an I/O operation to complete. |
| Data Plane CPU Utilization (%) | Data Plane CPU Utilization |
| Default Gateway | Default Gateway |
| Device Name | Device Name |
| Dropped (Packets) | Packets dropped: decapuslation error from control plane |
| Dropped Rate (Packets) | Packets dropped: decapuslation error from control plane |
| Family | Family |
| Free Memory (Kibibytes) | Free Memory |
| Global Protect Clientless VPN Version | Global Protect Clientless VPN Version |
| Global Protect Datafile Version | Global Protect Datafile Version |
| High Availability Anti-Virus Compatibility | High Availability Anti-Virus Compatibility |
| High Availability Application Content Compatibility | High Availability Application Content Compatibility |
| High Availability Control Link Port | High Availability Control Link Port |
| High Availability Data Link Port | High Availability Data Link Port |
| High Availability Enabled | High Availability Enabled |
| High Availability Global Protect Client Software Compatibility | High Availability Global Protect Client Software Compatibility |
| High Availability Management IP | High Availability Management IP |
| High Availability Management IPv6 | High Availability Management IPv6 |
| High Availability Mode | High Availability Mode |
| High Availability Passive Link State | High Availability Passive Link State |
| High Availability Peer IP | High Availability Peer IP |
| High Availability Peer IPv6 | High Availability Peer IPv6 |
| High Availability Peer Priority | High Availability Peer Priority |
| High Availability Preemptive | High Availability Preemptive |
| High Availability Priority | High Availability Priority |
| High Availability Software Version Compatibility | High Availability Software Version Compatibility |
| High Availability State | High Availability State |
| High Availability State Duration (Seconds) | High Availability State Duration |
| High Availability Threat Content Compatibility | High Availability Threat Content Compatibility |
| High Availability URL Compatibility | High Availability URL Compatibility |
| High Availability VPN Client Software Compatibility | High Availability VPN Client Software Compatibility |
| Hostname | Hostname |
| IP Address | IP Address |
| IPv6 Address | IPv6 Address |
| IPv6 Default Gateway | IPv6 Default Gateway |
| IPv6 Link Local Address | IPv6 Link Local Address |
| Is DHCP | Whether or not firewall uses Dynamic Host Configuration Protocol |
| Log Database Version | Log Database Version |
| MAC Address | MAC Address |
| Management Plane CPU Utilization (%) | Management Plane CPU Utilization |
| Maximum Supported Sessions (Sessions) | Maximum Supported Sessions |
| Memory Utilization (%) | Memory Utilization |
| Model | Model |
| Multi-VSYS | Multi Virtual Systems |
| Netmask | Netmask |
| Operational Mode | Operational Mode |
| Platform Family | Platform Family |
| Received From Control Plane (Packets) | Received From Control Plane |
| Received Throughput (Packets) | Received Throughput |
| Received Throughput Rate (Packets per Second) | Received Throughput |
| Running Tasks | Running Tasks |
| Sent Throughput (Packets) | Sent Throughput to host |
| Sent Throughput Rate (Packets per Second) | Sent Throughput to host |
| Serial | Serial |
| Session Throughput (Kibibytes per Second) | Session Throughput |
| Session Utilization (%) | Active sessions as a percent of maximum supported sessions |
| Sleeping Tasks | Sleeping Tasks |
| Software Version | Software Version |
| SSL HSM Events Received | The number of HSM up/down events received |
| SSL HSM Events Received Rate | The number of HSM up/down events received |
| Stopped Tasks | Stopped Tasks |
| Swap Cached Memory (Kibibytes) | Swap Cached Memory |
| Swap Free Memory (Kibibytes) | Swap Free Memory |
| Swap Total Memory (Kibibytes) | Swap Total Memory |
| Swap Used Memory (Kibibytes) | Swap Used Memory |
| Swap Utilization (%) | Swap Utilization |
| Threat Version | Threat Version |
| Total Memory (Kibibytes) | Total Memory |
| Total Tasks | Total Tasks |
| Transmitted to Control Plane (Packets) | Transmitted to Control Plane |
| Transmitted to Control Plane Rate (Packets per Second) | Transmitted to Control Plane |
| URL Filtering Version | URL Filtering Version |
| Used Memory (Kibibytes) | Used Memory |
| Users | Number of users |
| VM Mode | VM Mode |
| VM UUID | VM UUID |
| VPN Disable Mode | VPN Disable Mode |
| WildFire Private Version | WildFire Private Version |
| WildFire Version | WildFire Version |
| Zombie Tasks | Zombie Tasks |
Interface
| Name | Description |
|---|---|
| ARP Not Found | Logical interface ARP not found |
| CPU Errors (Errors) | Logical interface received errors from CPU |
| Data Dropped (Packets) | Logical interface packets dropped from CPU |
| Data Received (Packets) | Logical interface packets received from CPU |
| Duplex | Duplex |
| Errors Received (Errors) | Hardware interface errors received from CPU |
| Flow State Dropped Data (Packets) | Logical interface packets dropped by flow state check from CPU |
| Forwarding | Forwarding |
| Forwarding Errors (Errors) | Logical interface forwarding errors from CPU |
| Hardware Received Throughput (Bytes) | Hardware interface received throughput from CPU |
| Hardware Sent Throughput (Bytes) | Hardware interface sent throughput from CPU |
| ICMP Fragmentation | Logical interface ICMP fragmentation from CPU |
| ID | ID |
| IP Spoof Attacks | Logical interface IP spoof attacks from CPU |
| IPv4 Address | IPv4 Address |
| IPv6 Address | IPv6 Address |
| Layer 2 Decapsulated Data (Packets) | Logical interface layer 2 decapsulated packets from CPU |
| Layer 2 Encapsulated Data (Packets) | Logical interface layer 2 encapsulated packets from CPU |
| Local Area Network Denial Attacks | Logical interface LAN Denial attacks from CPU |
| Logical Received Throughput (Bytes) | Logical interface throughput received from CPU |
| Logical Sent Throughput (Bytes) | Logical interface sent throughput from CPU |
| MAC Address | MAC Address |
| MAC Not Found | Logical interface MAC not found from CPU |
| MAC Spoof Attacks | Logical interface MAC spoof attacks from CPU |
| Mode | Mode |
| Name | Name |
| Neighbor Info Pending | Logical interface neighbor info pending from CPU |
| Neighbor Not Found | Logical interface neighbor not found from CPU |
| No Route | Logical interface no route from CPU |
| Packets Dropped (Packets) | Hardware interface received packets dropped from CPU |
| Packets Received (Packets) | Hardware interface received packets from CPU |
| Packets Sent (Packets) | Logical interface packets sent from CPU |
| Physical Port Received Broadcast (Packets) | Physical port received broadcast from MAC |
| Physical Port Received Multicast (Packets) | Physical port received multicast from MAC |
| Physical Port Received Throughput (Bytes) | Physical port received throughput from MAC |
| Physical Port Received Unicast (Packets) | Physical port received unicast from MAC |
| Physical Port Sent Broadcast (Packets) | Physical port sent broadcast from MAC |
| Physical Port Sent Multicast (Packets) | Physical port sent multicast from MAC |
| Physical Port Sent Throughput (Bytes) | Physical port sent throughput from MAC |
| Physical Port Sent Unicast (Packets) | Physical port sent unicast from MAC |
| Ping-Of-Death Attacks | Logical interface ping-of-death attacks from CPU |
| Rated Speed | Rated Speed |
| Sent Packets (Packets) | Hardware interface sent packets from CPU |
| State | State |
| Tag | Tag |
| Teardrop Attacks | Logical interface MAC teardrop from CPU |
| Type | Type |
| Zone | Zone |
| Zone Changes | Logical interface zone change from CPU |
Policy Based Forwarding Table Rule
| Name | Description |
|---|---|
| Action | Action |
| Egress | Egress |
| Id | Id |
| Name | Name |
| Next Hop | Next Hop |
| Next Hop State | Next Hop State |
Power Rail
| Name | Description |
|---|---|
| Alarm | Alarm |
| Maximum Voltage (Volts) | Maximum Voltage |
| Minimum Voltage (Volts) | Minimum Voltage |
| Name | Name |
| Slot | Slot |
| Voltage (Volts) | Voltage |
Thermal Sensor
| Name | Description |
|---|---|
| Alarm | Alarm |
| Maximum Temperature (Celsius) | Maximum Temperature |
| Minimum Temperature (Celsius) | Minimum Temperature |
| Name | Name |
| Slot | Slot |
| Temperature (Celsius) | Temperature |
Virtual Router
| Name | Description |
|---|---|
| Equal-Cost Multi-Path Routing IPv4 Entries | Equal-Cost Multi-Path Routing IPv4 Entries |
| Equal-Cost Multi-Path Routing IPv6 Entries | Equal-Cost Multi-Path Routing IPv6 Entries |
| IPv4 Forwarding Table Entries | IPv4 Forwarding Table Entries |
| IPv4 Forwarding Table Entries Utilization (%) | Number of IPv4 forwarding table entries as a percent of max |
| IPv6 Forwarding Table Entries | IPv6 Forwarding Table Entries |
| IPv6 Forwarding Table Entries Utilization (%) | Number of IPv6 forwarding table entries as a percent of max |
| Maximum IPv4 Forwarding Table Entries | Maximum IPv4 Forwarding Table Entries |
| Maximum IPv6 Forwarding Table Entries | Maximum IPv6 Forwarding Table Entries |
| Name | Name |
VSYS
| Name | Description |
|---|---|
| Changes | Changes |
| Display Name | Display Name |
| Name | Name |
| Packet Throughput (Packets) | Packet Throughput |
| Sessions (Sessions) | Sessions |
| Threats | Threats |
| Throughput (Bytes) | Throughput |
Updated about 2 years ago
